THE PROBLEM
Zoom Bombing is exposing children learning remotely to inappropriate content and disrupting meetings so a few pranksters can have a laugh. The biggest unsolved issue with Zoom Bombing is that people are sharing links and passwords on social media in order to egg trolls and classmates on to bomb these classes and meetings. How can we share a meeting without disclosing the meeting ID and password?
THE SOLUTION

BombSquad is a solution I built on Amazon Web Services to help mitigate the worst of Zoom Bombing. Here’s how it works:
- Get a Zoom meeting invitation link like normal (and make sure the password feature is turned on!)
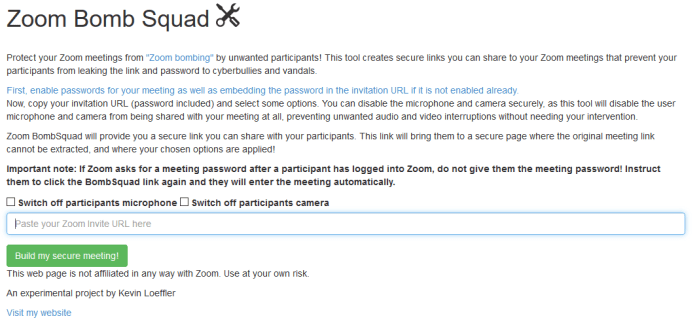
- Go to www.BombSquad.us
- Select your meeting options- you can permanently turn off the participant microphone and camera so that nobody can reenable it by clicking the checkboxes.
- Paste your invitation link
- Get a sharable cloaked URL that goes right to your meeting!
- Continue orchestrating your meeting from the Zoom client like normal.
The technical details are as follows: BombSquad takes your URL, transforms it to force the user to use the Zoom web client, stores the original URL securely, and only redirects the browser to the real meeting URL if the user clicks through the sharable link you receive. The invitation link inside the window is disabled. Thus, all a user can see are BombSquad URLs! This is performed using a combination of AWS S3 and Lambda instances as shown above, making this a neat example of a serverless application– the first I am distributing publicly!
SHARING THE SOLUTION
Head on over to www.bombsquad.us and give it a try!